Money Racing AV. Tracking a scareware affiliate
Since October 2011 we watch this affiliate system. Money Racing AV, a private PPS (Pay-Per-Sale) affiliate who spread actively fake antispywares (rogue). We have already seen this gang active in August 2009: A recent tour of scareware XII.Advertising can be found on various russian underground communities:
First contact with FTL (6 October 2011):
[14:29:33] Load4sales: hello
[14:30:02] mr: привет
[14:30:03] Load4sales: i'm late but just see your post on antichat about Money racing av v2
[14:30:25] mr: sorry bro
[14:30:26] mr: only for russians
[14:30:31] Load4sales: ah :/
[14:30:37] Load4sales: okay, thanks anyway
[14:30:46] mr: ok
[14:30:02] mr: привет
[14:30:03] Load4sales: i'm late but just see your post on antichat about Money racing av v2
[14:30:25] mr: sorry bro
[14:30:26] mr: only for russians
[14:30:31] Load4sales: ah :/
[14:30:37] Load4sales: okay, thanks anyway
[14:30:46] mr: ok
The money racing gang operate from moneyracing.ru. And are know to for spread scarewares who have this type of graphical user interface:
Money Racing website login:
The fish image is the logo of G-Loomis (a company, makers of fishing rods, reels, rod blanks and accessories), and probably a coincidence but during the 19th century there was the Loomis Gang.
A notorious family of outlaws that operated in central New York.
I've etablished the following structure of money racing site:
Moneyracing.ru - 64.191.20.101
moneyracing.ru/templates/images/
moneyracing.ru/uploads/
moneyracing.ru/test.php <- Malicious
moneyracing.ru/manual/ (Standard)
moneyracing.ru/icons/ (Standard)
moneyracing.ru/cgi-bin/ (Standard)
moneyracing.ru/chat/
moneyracing.ru/plugins/
moneyracing.ru/screens/
moneyracing.ru/logs/
moneyracing.ru/img/
moneyracing.ru/soft/
moneyracing.ru/fish/ <- iframe
moneyracing.ru/css/
moneyracing.ru/css/style.css (Guessed)
moneyracing.ru/css/admin.css (Guessed)
moneyracing.ru/geo/ (Standard)
moneyracing.ru/geo/geoip.inc (Standard)
moneyracing.ru//
moneyracing.ru/feed/
moneyracing.ru/back/
moneyracing.ru/stat/
moneyracing.ru/cron/
moneyracing.ru/captcha/
moneyracing.ru/javascripts/
moneyracing.ru/templates/images/
moneyracing.ru/uploads/
moneyracing.ru/test.php <- Malicious
moneyracing.ru/manual/ (Standard)
moneyracing.ru/icons/ (Standard)
moneyracing.ru/cgi-bin/ (Standard)
moneyracing.ru/chat/
moneyracing.ru/plugins/
moneyracing.ru/screens/
moneyracing.ru/logs/
moneyracing.ru/img/
moneyracing.ru/soft/
moneyracing.ru/fish/ <- iframe
moneyracing.ru/css/
moneyracing.ru/css/style.css (Guessed)
moneyracing.ru/css/admin.css (Guessed)
moneyracing.ru/geo/ (Standard)
moneyracing.ru/geo/geoip.inc (Standard)
moneyracing.ru//
moneyracing.ru/feed/
moneyracing.ru/back/
moneyracing.ru/stat/
moneyracing.ru/cron/
moneyracing.ru/captcha/
moneyracing.ru/javascripts/
From all these directories, some are interestings. Like the folder /back/
<img src="image.jpg" border="0" align="baseline" />
Last-Modified: Wed, 15 Jun 2011 10:19:41 GMT
Last-Modified: Wed, 15 Jun 2011 10:19:41 GMT
English translation:
Step 1.
Domain parking.
For starting the work you need park with us your domain on which all traffic will go.
For this setup your domain registar account DNS
ns1.dns.com
ns2.dns.com
After this, add domain for our parking in the Links section.
You can add few domains in same time, this will create a queue and if your domains goes banned it will be automatically replaced with new.
You can use request for automatic acquisition of fresh domain and replacing it in our TDS if you are using it.
**Domains which are banned removes from our DNS automatically.
Step 2.
Traffic Back URL
You should set URL "Traffic Back"
We will return surfer to you for to the indicated "Traffic Back" URL if
A. His OS and Browser does not match to us or if he was here in last 7 days.
B. Surfer went through our website and we redirects him back to yours "Traffic Back" URL
For non Adult traffic, average percent Exploited 18-20%, callhome 55-60%.
You earn 100% from 1000 USA installs. At the same time getting all your traffic back.
We accept only USA, WinXP, Vista, Win7, IE, FF.
All other traffic will be returned to your Back URL even before getting to our page.
Domain parking.
For starting the work you need park with us your domain on which all traffic will go.
For this setup your domain registar account DNS
ns1.dns.com
ns2.dns.com
After this, add domain for our parking in the Links section.
You can add few domains in same time, this will create a queue and if your domains goes banned it will be automatically replaced with new.
You can use request for automatic acquisition of fresh domain and replacing it in our TDS if you are using it.
**Domains which are banned removes from our DNS automatically.
Step 2.
Traffic Back URL
You should set URL "Traffic Back"
We will return surfer to you for to the indicated "Traffic Back" URL if
A. His OS and Browser does not match to us or if he was here in last 7 days.
B. Surfer went through our website and we redirects him back to yours "Traffic Back" URL
For non Adult traffic, average percent Exploited 18-20%, callhome 55-60%.
You earn 100% from 1000 USA installs. At the same time getting all your traffic back.
We accept only USA, WinXP, Vista, Win7, IE, FF.
All other traffic will be returned to your Back URL even before getting to our page.
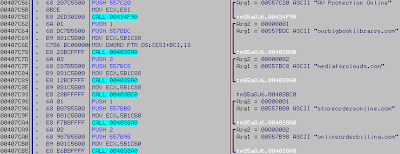
And if we go back in 2009 we can see that these scarewares connect directly to moneyracing.ru:
Malware MD5: E1EEDEEF721D6F87FFB0E1EC9CEE9F95
urls found inside:
Scareware GUI:
Now if we do a simple brain reflexion on 'Racing Money'
Money... Alright!
Racing... hmm what.. racing = cars
And if we check the old IP used in years 200..
we found lanos-club.ru a forum about cars, maybe it's just a coincidence.
Back about the moneyracing.ru domain, we have also this 'test.php' a malicious page detected as Blackhole Exploit Kit, (probably very old)
Obfuscated code lead to xmlalien.in/main.php?page=1321edc7470b347f
Now, what's the IP of money racing can told us:
The 302/403 responses of DNS are interesting because they return the name of machines
for example, on the money racing network: orderonline-1.com was used as billing machine.
Machine name: bill.host
orderonline-1.com/cgi-bin/
orderonline-1.com/images/
orderonline-1.com/admin/
orderonline-1.com/icons/
orderonline-1.com/signup/
orderonline-1.com/manual/
orderonline-1.com/sig/
orderonline-1.com/css/
orderonline-1.com/js/
orderonline-1.com/%2523FFFFFF/
orderonline-1.com/%2523999999/
orderonline-1.com/cron/
orderonline-1.com/cgi-bin/
orderonline-1.com/images/
orderonline-1.com/admin/
orderonline-1.com/icons/
orderonline-1.com/signup/
orderonline-1.com/manual/
orderonline-1.com/sig/
orderonline-1.com/css/
orderonline-1.com/js/
orderonline-1.com/%2523FFFFFF/
orderonline-1.com/%2523999999/
orderonline-1.com/cron/
And freshmediacontent.com as report machine:
Machine name: reports.host
freshmediacontent.com/admin/home/login
freshmediacontent.com/admin/home/logout
freshmediacontent.com/admin/members
freshmediacontent.com/admin/settings
freshmediacontent.com/admin/logs
freshmediacontent.com/admin/home/login
freshmediacontent.com/admin/home/logout
freshmediacontent.com/admin/members
freshmediacontent.com/admin/settings
freshmediacontent.com/admin/logs
I've recontacted the owner of money racing on 09 December 2011:
Out of business apparently and according to him.
He told me to search on undergrounds forum a guys with the nick: 'бомбе'
But i've never find a 'Bomb' or someone else affiliated with money racing, so i've again contacted him, 18 December 2011:
Even with attractive USA traffics and all the requierement, he keep to tell me to search 'бомбе'
But it's more probable that he don't want partners for the moment due to the exposure of Vyacheslav Zakorzhevsky made in October 27.
Now more recently, in January, a colleague detected the domain core6575.opensourceavpro.com as malicious download, but the domain in question is from the money racing network.
• dns: 1 » ip: 213.133.100.207 - adresse: CORE6575.OPENSOURCEAVPRO.COM
Domain name: OPENSOURCEAVPRO.COM
Name Server: dns1.opensourceavpro.com 213.133.100.207
Name Server: dns2.opensourceavpro.com 213.133.100.207
Creation Date: 2011.10.18
Updated Date: 2011.12.01
Expiration Date: 2012.10.18
Status: DELEGATED
Registrant ID: GDZ6YAX-RU
Registrant Name: Oleg Stoyanov
Registrant Organization: Oleg Stoyanov
Registrant Street1: Botanicheskaya 8
Registrant City: Moscow
Registrant Postal Code: 127276
Registrant Country: RU
Administrative, Technical Contact
Contact ID: GDZ6YAX-RU
Contact Name: Oleg Stoyanov
Contact Organization: Oleg Stoyanov
Contact Street1: Botanicheskaya 8
Contact City: Moscow
Contact Postal Code: 127276
Contact Country: RU
Contact Phone: +7 495 5468308
Contact E-mail: olegstoyanov@hotmail.com
Registrar: Regional Network Information Center, JSC dba RU-CENTER
Domain name: OPENSOURCEAVPRO.COM
Name Server: dns1.opensourceavpro.com 213.133.100.207
Name Server: dns2.opensourceavpro.com 213.133.100.207
Creation Date: 2011.10.18
Updated Date: 2011.12.01
Expiration Date: 2012.10.18
Status: DELEGATED
Registrant ID: GDZ6YAX-RU
Registrant Name: Oleg Stoyanov
Registrant Organization: Oleg Stoyanov
Registrant Street1: Botanicheskaya 8
Registrant City: Moscow
Registrant Postal Code: 127276
Registrant Country: RU
Administrative, Technical Contact
Contact ID: GDZ6YAX-RU
Contact Name: Oleg Stoyanov
Contact Organization: Oleg Stoyanov
Contact Street1: Botanicheskaya 8
Contact City: Moscow
Contact Postal Code: 127276
Contact Country: RU
Contact Phone: +7 495 5468308
Contact E-mail: olegstoyanov@hotmail.com
Registrar: Regional Network Information Center, JSC dba RU-CENTER
By searching infos and urls we can determine the following syntax:
core6575.opensourceavpro.com/?RID=2671/terms.html
This domain was used as landing page for money racing partners.
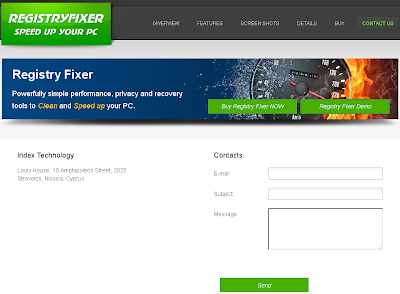
A screenshot of the site:
From the cascading style sheets of the site I've found also an image who is absolutely not related with the usual scareware landing:
But i've found nothing related to a 'Youtube Studio' landing page on the server
but with Google i get this: youtubestudiopro.com.
Downloaded file is legit:
MD5: D3A748372338841FCD4366307F3EE657
The graph of youtubestudiopro.com is interesting:
Detail for 64.120.214.18:
Pharma domains, payment processors...
And if i click on contact: 64.79.111.19/contacts.html. Another landing page, this time 'Monstocloud':
The company adress is the same a Registry Fixer (egistryengineer.com):
Now for return to core6575.opensourceavpro.com, there is just a scareware hosted 'setup.exe' (AV Protection Online).
Malware MD5: 45BFC0DE3C78454B8C80623B7DE965B0
As usual we can have the machines name with 302 or 403 requests.
ourbigbooklibrarry.com and mediaforclouds.com as "reports.host".

storeordersonline.com and onlineorderbilling.com as "bill.host".

Also note that this '360 Security' was never found as 'executable version'
opensourceavpro.com have also a fake purchase page online
Even the captcha is a fake (a static GIF image) and not verified:
When we do a wrong billing order, the following text is displayed:
Sorry, please contact as by email: support@ccbil-payment.com
CCBill, is a payment processing service, mostly used for Adult.
We have also this url from opensourceavpro.com, once again related with the money racing network:
avsecurecs.com
• dns: 1 » ip: 212.124.122.144 - adresse: AVSECURECS.COM
Domain name: AVSECURECS.COM
Name Server: dns1.avsecurecs.com 213.133.100.207
Name Server: dns2.avsecurecs.com 213.133.100.207
Creation Date: 2011.08.03
Updated Date: 2011.12.18
Expiration Date: 2012.08.03
Status: DELEGATED
Registrant ID: PBU1LTD-RU
Registrant Name: Cyprus company
Registrant Organization: Cyprus company
Registrant Street1: 6 Karaiskakis Street
Registrant City: Limassol
Registrant Postal Code: 53034
Registrant Country: CY
Administrative, Technical Contact
Contact ID: PBU1LTD-RU
Contact Name: Cyprus company
Contact Organization: Cyprus company
Contact Street1: 6 Karaiskakis Street
Contact City: Limassol
Contact Postal Code: 53034
Contact Country: CY
Contact Phone: +357 25555000
Contact E-mail: tomronalds@hotmail.com
Registrar: Regional Network Information Center, JSC dba RU-CENTER
• dns: 1 » ip: 212.124.122.144 - adresse: AVSECURECS.COM
Domain name: AVSECURECS.COM
Name Server: dns1.avsecurecs.com 213.133.100.207
Name Server: dns2.avsecurecs.com 213.133.100.207
Creation Date: 2011.08.03
Updated Date: 2011.12.18
Expiration Date: 2012.08.03
Status: DELEGATED
Registrant ID: PBU1LTD-RU
Registrant Name: Cyprus company
Registrant Organization: Cyprus company
Registrant Street1: 6 Karaiskakis Street
Registrant City: Limassol
Registrant Postal Code: 53034
Registrant Country: CY
Administrative, Technical Contact
Contact ID: PBU1LTD-RU
Contact Name: Cyprus company
Contact Organization: Cyprus company
Contact Street1: 6 Karaiskakis Street
Contact City: Limassol
Contact Postal Code: 53034
Contact Country: CY
Contact Phone: +357 25555000
Contact E-mail: tomronalds@hotmail.com
Registrar: Regional Network Information Center, JSC dba RU-CENTER
Screenshot of avsecurecs.com:
Customer area:
On the "About Us" page they claim to be at 392 Potrero Avenue, Sunnyvale.
But 360 Security LP don't exist:
We have also found a phpinfo file on the server.
And get interesting informations:
SSH_CONNECTION 212.124.122.134 60463 176.31.230.169 22
System Linux ns226633.ovh.net 2.6.38.2-grsec-xxxx-grs-ipv6-64 #2 SMP Thu Aug 25 16:40:22 UTC 2011 x86_64
SCRIPT_FILENAME /home/sites/st2/html/chat/php.php
SCRIPT_URI http://st2.host/chat/php.php
SCRIPT_URL /chat/php.php
SERVER_ADDR 176.31.230.169
SERVER_ADMIN root@238072.b128.hostseek.ru
System Linux ns226633.ovh.net 2.6.38.2-grsec-xxxx-grs-ipv6-64 #2 SMP Thu Aug 25 16:40:22 UTC 2011 x86_64
SCRIPT_FILENAME /home/sites/st2/html/chat/php.php
SCRIPT_URI http://st2.host/chat/php.php
SCRIPT_URL /chat/php.php
SERVER_ADDR 176.31.230.169
SERVER_ADMIN root@238072.b128.hostseek.ru
Actual domain of money racing is mrwrk.com, mrwrk stand probably for "Money racing workers"
Domain name: MRWRK.COM
Name Server: dns1.mrwrk.com 212.124.122.144
Name Server: dns2.mrwrk.com 212.124.122.144
Creation Date: 2011.05.18
Updated Date: 2011.11.01
Expiration Date: 2012.05.18
Status: DELEGATED
Registrant ID: YWAAUUH-RU
Registrant Name: Kiborg Solutions LLC
Registrant Organization: Kiborg Solutions LLC
Registrant Street1: shevchenko 12
Registrant City: Kiev
Registrant Postal Code: 30015
Registrant Country: UA
Administrative, Technical Contact
Contact ID: YWAAUUH-RU
Contact Name: Kiborg Solutions LLC
Contact Organization: Kiborg Solutions LLC
Contact Street1: shevchenko 12
Contact City: Kiev
Contact Postal Code: 30015
Contact Country: UA
Contact Phone: +380 44 4907681
Contact E-mail: soknosergei@yahoo.com
Registrar: Regional Network Information Center, JSC dba RU-CENTER
Name Server: dns1.mrwrk.com 212.124.122.144
Name Server: dns2.mrwrk.com 212.124.122.144
Creation Date: 2011.05.18
Updated Date: 2011.11.01
Expiration Date: 2012.05.18
Status: DELEGATED
Registrant ID: YWAAUUH-RU
Registrant Name: Kiborg Solutions LLC
Registrant Organization: Kiborg Solutions LLC
Registrant Street1: shevchenko 12
Registrant City: Kiev
Registrant Postal Code: 30015
Registrant Country: UA
Administrative, Technical Contact
Contact ID: YWAAUUH-RU
Contact Name: Kiborg Solutions LLC
Contact Organization: Kiborg Solutions LLC
Contact Street1: shevchenko 12
Contact City: Kiev
Contact Postal Code: 30015
Contact Country: UA
Contact Phone: +380 44 4907681
Contact E-mail: soknosergei@yahoo.com
Registrar: Regional Network Information Center, JSC dba RU-CENTER
mrwrk and SSH connections was under brute force (pure and with wordlists) but that have done nothing. This gang continue to make errors and we will continue to keep an eye on.
Steven K (Xylitol)
Malware Research



































1 comentarios:
Great Job Xyli.. Kudos :)
Post a Comment