Intelligence and operational level by Siberia Exploit Pack
Siberia Exploit Pack is a crimeware, evolution of Napoleon Exploit Pack, which we've done a brief description on another occasion. However, since the time of that description to this day, the landscape has expanded its developer.
In this regard, and while it ends up being one of the bunch, the interesting thing about this crimeware is information provided by their panel of statistics (intelligence for the attacker), by the way very similar to that provided by Eleonore Exploit Pack, which provide data regarding the success of business which has the exploit pack for recruitment zombie, discriminating on the basis of these data:
- Countries affected
- Most exploited Operating Systems
- Reference domains with the highest percentage by which vulnerabilities are exploited
- Browsers exploited
- Pre-compiled exploits in this version of the package
Let me stress (because it's a minor detail) with this collection of information is nothing more than to intelligence, which allows the attacker to know, at first instance:
In the former case, the population of which country is more vulnerable, perhaps because of their level of piracy, which brings to attention the lack of security updates for operating systems and applications, because as we will see to reach exploits, all these are known and have long been concerned with the patch that fixes the vulnerability.
In this case, the first five countries where this crimeware has higher infection rate include the United States, Britain, Canada, Russia and Germany.
In the former case, the population of which country is more vulnerable, perhaps because of their level of piracy, which brings to attention the lack of security updates for operating systems and applications, because as we will see to reach exploits, all these are known and have long been concerned with the patch that fixes the vulnerability.
In this case, the first five countries where this crimeware has higher infection rate include the United States, Britain, Canada, Russia and Germany.
The same approach is being pursued with the data we obtained on operating systems "vulnerable" in quotes because, as I said above, the degree of vulnerability of the OS depends directly on a number of aspects that should be covered by hardening, in which an important factor is the implementation of security patches.
For example, the vulnerability in MDAC (Microsoft Data Access Components) from the year 2006 (four years), described in Microsoft Official Bulletin MS06-014. The impact on operating systems have this version of crimeware, we can see in the picture below.
For example, the vulnerability in MDAC (Microsoft Data Access Components) from the year 2006 (four years), described in Microsoft Official Bulletin MS06-014. The impact on operating systems have this version of crimeware, we can see in the picture below.
The list of operating systems is large and attacked the three with the highest vulnerability gap belongs to the family of Microsoft (which is obviously due to the massiveness of use), and other MS also.
However, the crimeware cover other non-Windows operating systems, including PlayStation consoles (GNU / Linux or Black Rhino) and Nintendo Wii (ironically a modified version of a GNU/Linux), in the case of OS used and Workstations high-end mobile phones, including:
However, the crimeware cover other non-Windows operating systems, including PlayStation consoles (GNU / Linux or Black Rhino) and Nintendo Wii (ironically a modified version of a GNU/Linux), in the case of OS used and Workstations high-end mobile phones, including:
- Mac OS
- GNU/Linux
- FreeBSD
- iPhone
- Windows Mobile
- Windows CE
- Pocket PC
- Symbian OS
Here we are beginning to recognize that criminals have broadened the scope of coverage, incorporating into its portfolio of options exploitation of vulnerabilities (through the browser) and recruitment of zombies on other operating systems used in other computer technologies.
Regarding references, involving nearly 28.000 domains where each of them redirect to another page with malicious content or at least doubtful as:
Regarding references, involving nearly 28.000 domains where each of them redirect to another page with malicious content or at least doubtful as:
- Pornographic Pages
- Scareware propagation (or rogue) and other types of malicious code - c76a8a1171f5ae82a647ddda7071db1f - 5050804b1eea9e175c6a47e6589d36c4 -
- Scam
- Search engines (Google, Yahoo, Bing, yadex)
- Online Pharma
- Online Casinos
References to these sites are obtained through an application of such TDS (Traffic Distribution System), also installed on the same server, used to redirect traffic to and from the pages listed in this module of the package. The TDS are widely used for BlackHat SEO.
Moreover, the list is very large as it details the most violated browsers together with their respective versions, they are:
Moreover, the list is very large as it details the most violated browsers together with their respective versions, they are:
- Internet Explorer since version 4 through 8
- Firefox from version 1.0.3 to 3.6b4
- Opera from version 6.0 to 10.0
- Opera for Mobile
- Safari browser
- PlayStation (Firefox)
- Pocket PC
- SeaMonkey 1.1 and 2.0 (Mozilla Suite, which includes a web browser)
- Nintendo browser
- IPhone Browser
- Mobile Phone Browser (Internet Explorer)
- Chrome from version 1.0 to 6.0
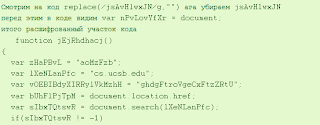
Finally, what are the exploit managers exploit vulnerabilities in all of the above? Well, in principle it should be noted that it's the exploits are designed to exploit known vulnerabilities, as I mentioned above, long-standing.
The most exploited, Java GSB. Less exploited vulnerabilities are those of Adobe Reader PDF files through manipulated.
The most exploited, Java GSB. Less exploited vulnerabilities are those of Adobe Reader PDF files through manipulated.
Undoubtedly the cybercriminals intelligence processes incorporate in their strategies to spread / infection, allowing them to have a comprehensive picture of the situation on the virtual field, increasing the successful outcome in their attacks.
Imagine this data to run campaigns on a "virtual guerrilla war", even to understand the variety of OS environments used in military/government and analyze well the best place to carry out DDoS attacks against critical resources of a State. The thing does not seem so trivial.
Jorge Mieres
Founder & Director of MalwareIntelligence
Crimeware & Intelligence Analyst Researcher
Related information
State of the art in CRiMEPACK Exploit PackImagine this data to run campaigns on a "virtual guerrilla war", even to understand the variety of OS environments used in military/government and analyze well the best place to carry out DDoS attacks against critical resources of a State. The thing does not seem so trivial.
Jorge Mieres
Founder & Director of MalwareIntelligence
Crimeware & Intelligence Analyst Researcher
Related information
Crimeware-as-a-Service and antivirus evasion schemes
Russian service online to check the detection of malware
Software as a Service on the malware industry
Creating Online PoisonIvy based polymorphic malware Ver más